- Package workflows
- View packages
- Authenticate with the registry
- Use GitLab CI/CD to build packages
- Reduce storage usage
- Disable the Package Registry
- Package Registry visibility permissions
- Accepting contributions
Package Registry
Moved from GitLab Premium to GitLab Free in 13.3.
With the GitLab Package Registry, you can use GitLab as a private or public registry for a variety of supported package managers. You can publish and share packages, which can be consumed as a dependency in downstream projects.
Package workflows
Learn how to use the GitLab Package Registry to build your own custom package workflow:
-
Use a project as a package registry to publish all of your packages to one project.
-
Publish multiple different packages from one monorepo project.
View packages
You can view packages for your project or group.
- Go to the project or group.
- Go to Packages and registries > Package Registry.
You can search, sort, and filter packages on this page. You can share your search results by copying and pasting the URL from your browser.
You can also find helpful code snippets for configuring your package manager or installing a given package.
When you view packages in a group:
- All projects published to the group and its projects are displayed.
- Only the projects you can access are displayed.
- If a project is private, or you are not a member of the project, it is not displayed.
For information on how to create and upload a package, view the GitLab documentation for your package type.
Authenticate with the registry
Authentication depends on the package manager being used. For more information, see the docs on the specific package format you want to use.
For most package types, the following credential types are valid:
- Personal access token: authenticates with your user permissions. Good for personal and local use of the package registry.
- Project deploy token: allows access to all packages in a project. Good for granting and revoking project access to many users.
- Group deploy token: allows access to all packages in a group and its subgroups. Good for granting and revoking access to a large number of packages to sets of users.
- Job token: allows access to packages in the project running the job for the users running the pipeline. Access to other external projects can be configured.
- If your organization uses two factor authentication (2FA), you must use a personal access token with the scope set to
api. - If you are publishing a package via CI/CD pipelines, you must use a CI job token.
Use GitLab CI/CD to build packages
You can use GitLab CI/CD to build packages.
For Maven, NuGet, npm, Conan, Helm, and PyPI packages, and Composer dependencies, you can
authenticate with GitLab by using the CI_JOB_TOKEN.
CI/CD templates, which you can use to get started, are in this repository.
Learn more about using the GitLab Package Registry with CI/CD:
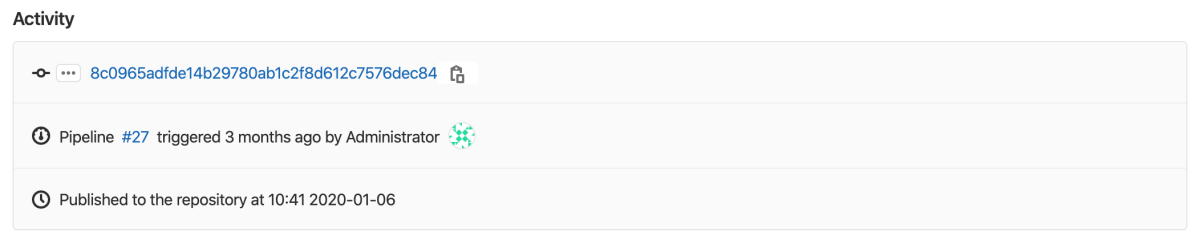
If you use CI/CD to build a package, extended activity information is displayed when you view the package details:
You can view which pipeline published the package, and the commit and user who triggered it. However, the history is limited to five updates of a given package.
Reduce storage usage
For information on reducing your storage use for the Package Registry, see Reduce Package Registry storage use.
Disable the Package Registry
The Package Registry is automatically enabled.
If you are using a self-managed instance of GitLab, your administrator can remove the menu item, Packages and registries, from the GitLab sidebar. For more information, see the administration documentation.
You can also remove the Package Registry for your project specifically:
- In your project, go to Settings > General.
- Expand the Visibility, project features, permissions section and disable the Packages feature.
- Select Save changes.
The Packages and registries > Package Registry entry is removed from the sidebar.
Package Registry visibility permissions
Project-level permissions determine actions such as downloading, pushing, or deleting packages.
The visibility of the Package Registry is independent of the repository and can be controlled from your project’s settings. For example, if you have a public project and set the repository visibility to Only Project Members, the Package Registry is then public. Disabling the Package Registry disables all Package Registry operations.
| Project visibility | Action | Role required |
|---|---|---|
| Public | View Package Registry |
n/a, everyone on the internet can perform this action
|
| Public | Publish a package | Developer or higher |
| Public | Pull a package |
n/a, everyone on the internet can perform this action
|
| Internal | View Package Registry | Guest or higher |
| Internal | Publish a package | Developer or higher |
| Internal | Pull a package | Guest or higher(1) |
| Private | View Package Registry | Reporter or higher |
| Private | Publish a package | Developer or higher |
| Private | Pull a package | Reporter or higher(1) |
Allow anyone to pull from Package Registry
Introduced in GitLab 15.7 with a flag named package_registry_access_level. Enabled by default.
package_registry_access_level.If you want to allow anyone (everyone on the internet) to pull from the Package Registry, no matter what the project visibility is, you can use the additional toggle Allow anyone to pull from Package Registry that appears when the project visibility is Private or Internal.
Several known issues exist when you allow anyone to pull from the Package Registry:
- Project-level endpoints are supported. Group-level and instance-level endpoints are not supported. Support for group-level endpoints is proposed in issue 383537.
- It does not work with the Composer, because Composer only has a group endpoint.
- It works with Conan, but using
conan searchdoes not work.
Accepting contributions
This table lists unsupported package manager formats that we are accepting contributions for. Consider contributing to GitLab. This development documentation guides you through the process.
| Format | Status |
|---|---|
| Chef | #36889 |
| CocoaPods | #36890 |
| Conda | #36891 |
| CRAN | #36892 |
| Opkg | #36894 |
| P2 | #36895 |
| Puppet | #36897 |
| RPM | #5932 |
| SBT | #36898 |
| Swift | #12233 |
| Vagrant | #36899 |